In Crowdstrike’s original announcement that “Russia” had hacked the DNC, Dmitri Alperovitch said, on the one hand, that the “tradecraft” of the hackers was “superb” and their “operational security second none” and, on the other hand, that Crowdstrike had “immediately identified” the “sophisticated adversaries”. In contrast, after three years of investigation of Climategate, UK counter-intelligence had been unable to pin down even whether the hacker was a lone motivated individual or organized foreign intelligence service. Mr FOIA of Climategate subsequently emailed several bloggers, including myself, stating that he was a lone individual outside the UK who was a keen reader of Climate Audit and WUWT – a claim that I accept and which is consistent with my own prior interpretation of Climategate data and metadata.
I draw the contrast to draw attention to the facial absurdity of Crowdstrike’s claim that the tradecraft of the DNC hackers was “superb” – how could it be “superb” if Crowdstrike was immediately able to attribute them?
In fact, when one looks more deeply into the issue, it would be more accurate to say that the clues left by the DNC hackers to their “Russian” identity were so obvious as to qualify for inclusion in the rogue’s gallery of America’s Dumbest Criminals, criminals like the bank robber who signed his own name to the robbery demand.
To make matters even more puzzling, an identically stupid and equally provocative hack, using an identical piece of software, had been carried out against the German Bundestag in 2015. A further common theme to the incidents is that both resulted in a dramatic deterioration of relations with Russia – between Germany and Russia in 2015 and USA and Russia in 2016-2017.
Perhaps it’s time to ask “Cui bono?” and re-examine the supposedly “superb tradecraft”. I’ll begin today’s story, perhaps appropriately, with a Nigerian phishing scam.
Nigerian Phishing Scams
By now, everyone should be aware of Nigerian phishing scams, which are almost as old as the internet. The scammers set up websites with names resembling legitimate sites, then try to steal credentials through phishing emails. aa419.org contains a voluntary list of fake sites – the screenshot below shows only the first few entries in their list of fake “Paypal” sites.
Over the years, aa419.0rg collected whois information on fake websites. For example, their page on the fake website www.londoncitybankplc[.]com shows that its administrative contact supposedly resides on Cloverdale Lane in DeSoto, Texas and can be contacted at email adeweb2001[@]yahoo.com.
A search of their database on the contact email yields a total of registrations, the most recent of which is http://www.cbiuaebank[.]com, added to their database on May 28, 2015.
A search of the aa419 database on “cloverdale” resulted in 33 matches, the most recent of which are shown in the screenshot below.
The root9b Report, May 10, 2015
On May 10, 2015, root9b, a cybersecurity firm in Colorado, released a dramatic report entitled “APT28 targets financial markets: root9b releases zero day hashes”. It began by raising alarm over the “threat posed by Russian hacking groups”:
Cybersecurity experts are increasingly concerned about the threat posed by Russian hacking groups… The increase in cyber-exploits is also accompanied by a much more aggressive Russian foreign policy, which has seen them invade Ukraine and literally seize control of sovereign territory in Crimea. So it should not surprise anyone that just as nuclear capable Russian bombers are increasingly penetrating foreign airspace, their cyber-warriors appear to be ramping up their intrusions as well.
They then described how their “firm of cybersecurity experts, staffed by veterans from the United States Department of Defense” had “uncovered a global attack in the making, and took steps to protect not only our clients, but other identified victims as well”. The adversary who they had thwarted was identified as APT28 (Crowdstrike’s Fancy Bear), who they identified as a “particularly prolific and superbly talented group of Russian hackers, which has strongly suspected ties to Russian intelligence services”.
root9B espoused a philosophy, later also promoted by Crowdstrike:
To combat threats, root9B realized that technology is not the problem. “Computers don’t attack networks. People do,” said root9B.
root9B said that, in late April 2015, while analysts were carrying out routine security analysis, they “discovered what appeared to be a targeted spearphishing domain aimed at a financial institution”, in the process discovering malware historically “unique” to APT28/Fancy Bear (Sofacy):
As analysts continued their work they discovered several more pieces of new malware. The malicious code bore specific signatures that have historically been unique to only one organization, Sofacy. This malware was pointing at a spearfishing domain registered to impersonate a Middle Eastern financial institution and the domain registration details did not match normal Sofacy operational signatures. That said, the malicious software certainly did.
root9B said that they “initially noted that one in particular, CBIUAEBANK COM, appeared to be a fake version of CBIUAE.COM, the actual domain of the website of Commercial Bank International of the United Arab Emirates.”
Root9B said that, as they analysed the metadata, they noticed a “mistake”, a “very unique signature”:
As root9B analyzed increasing amounts of metadata and associated indicators, they were able to identify a very unique signature consistently used by someone involved in setting up the hack….The discovery of the hacker’s single mistake in tradecraft was indeed a powerful catalyst, and lead to the discovery of a treasure trove of new indicators.
The “mistake” in supposedly “superb” Russian tradecraft that had been spotted by root9b was that registrants for the fake websites all used addresses on Cloverdale Lane in DeSoto, Texas:
All of the fictitious personalities list the same street address. While they change names and house numbers for them, they all reside on Cloverdale Lane in DeSoto, Texas.
root9B proclaimed that this mistake was a “a common thread which unraveled all of Sofacy’s careful preparation”. root9B listed a series of domains which were being marshaled by APT28/Fancy Bear: cbibuae[.]com, cbiuaeonline[.]c0m, etc. They also warned of other linked fake domains from other organizations including T-D-canadatrust[.]com.
In addition to the fake websites, root9b also announced the discovery of new “indicators of malware”:
In addition to identifying targets, root9B analysts also discovered indicators of malware, the analysis of which revealed several zero-day threats and their corresponding “hashes.” Each new discovery revealed more information, enabling a more complete picture to emerge.
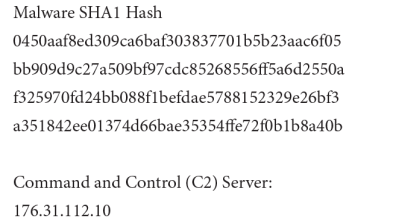
They issued an urgent warning that “it is recommended that networks begin
blocking the following hashes [shown below] and communications with the identified Command and Control (C2) server” 176.31.112[.]10]:
As I’ll discuss in a subsequent post, the C2 server 176.31.112[.]10 turns out to have a central role in establishing “Russian” responsibility for the DNC hack, a role which has thus far not been critically examined.
The root9B report was widely publicized, including reports by Fox News, Politico, SC Magazine and The Hill – all of whom amplified the increasing “Russian” threat.
Krebs, May 20, 2015
The connection of root9B’s indicators of compromise to Nigerian phishing scams was almost immediately (May 20, 2015) noticed by Krebs On Security here. Krebs stated that the only actual connection between Sofacy (APT28/Fancy Bear) and the fake bank domains was that the “fake bank domains used a domain name server previously associated with Sofacy activity: carbon2u[dot]com”. However, Krebs observed that “there is plenty of other badness unrelated to Sofacy that calls Carbon2u home for their DNS operations” and concluded that the “vast majority” of the root9B report merely documented “run-of-the-mill” Nigerian scamming:
From what I can tell, the vast majority of the report documents activity stemming from Nigerian scammers who have been conducting run-of-the-mill bank phishing scams for almost a decade now and have left quite a trail.
Krebs observed that the
most of the wordage in this report from root9B discusses fake domains registered to a handful of email addresses, including “adeweb2001@yahoo.com,” adeweb2007@yahoo.com,” and “rolexzad@yahoo.com”.
Each of these emails have long been associated with phishing sites erected by apparent Nigerian scammers. They are tied to this Facebook profile for a Showunmi Oluwaseun, who lists his job as CEO of a rather fishy-sounding organization called Rolexzad Fishery Nig. Ltd.
The domain rolexad[dot]com was flagged as early as 2008 by aa419.org, a volunteer group that seeks to shut down phishing sites — particularly those emanating from Nigerian scammers (hence the reference to the Nigerian criminal code 419, which outlaws various confidence scams and frauds). That domain also references the above-mentioned email addresses. Here’s another phishy bank domain registered by this same scammer, dating all the way back to 2005!
The presently online version of the root9B report does not mention any of these email addresses – I presume that the root9B report has been altered. The “phishy bank domain” linked by Krebs is the fake website www.londoncitybankplc[.]com discussed above. In addition to the associations between fake websites arising from registrar email addresses mentioned by Krebs, there is the association between fake Nigerian websites arising from “Cloverdale Lane”, the supposed centerpiece of the root9B analysis.
Krebs interviewed Jaime Blasco, the chief scientist at Alien Vault, an authority on APT28/Sofacy, who confirmed Krebs’ opinion that the research was “very poor”. Blasco opined that the document seemed more like a “marketing report” seeking “media coverage”:
Actually, there isn’t a link between what root9B published and Sofacy activity,” he said. “The only link is there was a DNS server that was used by a Sofacy domain and the banking stuff root9B published. It doesn’t mean they are related by any means. I’m really surprised that it got a lot of media attention due to the poor research they did, and [their use] of [terms] like ‘zeroday hashes’ in the report really blew my mind. Apart from that it really looks like a ‘marketing report/we want media coverage asap,’ since days after that report they published their Q1 financial results and probably that increased the value of their penny stocks.”
root9B Postscript
On June 15, pseudonymous Pump Stopper wrote a savage investor review of root9b, stating that it had no valid technology or business, had an “unsustainable valuation of $140m+” and a “-82.5% downside”. Pump Stopper under-estimated root9B’s downside: its current market capitalization is now down to $5 million and, at present cash burn, is insolvent.
On January 4, 2016, a class action lawsuit was filed against root9B by investors who alleged that root9B’s officers and directors had made material misrepresentations, including false claims to have detected a ” sophisticated state-sponsored Russian hacking attack”. (The lawsuit cited both the original report and Krebs’ analysis at length.)
The misrepresentations were false because, according to the Company’s own reports filed in 2015, it did not sell “proprietary” hardware and software but was a reseller of another company’s product. Further, root9B did not detect a sophisticated state-sponsored Russian hacking attack but rather a routine “phishing” scheme operated by Nigerian scammers. Defendants Grano and Smith were fully aware of the non-proprietary nature of the hardware sold by root9B as well as the actual details of the hacking attack attributed to Sofacy/APT28 yet nonetheless made the misrepresentations to the public.
root9B raised $11.4 million in stock offerings in first quarter 2015. This is a fraction of Crowdstrike’s money raising and valuation: it’s raised $256 million and was valued at just under $1 billion in May 2017.
Next Post
In the next post in this story, I’ll follow the story of the C2 malware indicator (176.31.112[.]10]) discovered by root9B in their unwitting investigation of Nigerian bank scams.








108 Comments
Stephen,
This article may be of interest in this matter
View at Medium.com
Both Kaspersky and Semantic demolished Alperovitch’s work in 2011: he was a shoddy rat https://eugene.kaspersky.com/2011/08/18/shady-rat-shoddy-rat/ https://www.symantec.com/connect/blogs/truth-behind-shady-rat
In the end it was the US IC’s report of January 6 2017 that underlined the “Russia, Russia” hype https://www.dni.gov/files/documents/ICA_2017_01.pdf
Why were they so desperate to approve that feeble claim? Guilt, deception, politics, fear …?
This post says:
There is no contradiction between exhibiting superb tradecraft and being readily identifiable. In fact, sometimes the two go hand-in-hand. Being really good at what you do can be part of what makes it so easy to recognize your handiwork.
Consider the burglar who is really good at bypassing a particular type of security system. He may do a good job breaking into a place, leave no evidence that could identify him or allow him to be prosecuted, but that doesn’t mean the police would be unable to associate him with other burglaries he committed.
Brandon, you make me smile. You are claiming that a skilful hacker who expertly leaves no clues to his identity, can be identified by the fact that he can’t be identified.
Brandon, I haven’t finished my story yet, but that’s not the case here. I’ll show that it’s more like America’s Dumbest Criminals – a comparison that was previously made at CA in connection with Peter Gleick putting his own name in the forged Heartland memorandum, catnip to Mosher.
If by “here” you are referring to the primary story in this post, I should point out I am quite familiar with this case. I’ve been aware of root9B for years. It’s a bad company. It’s work is, charitably speaking, shoddy. Two years ago, I decided the company went beyond mere incompetence and went into outright dishonesty.
But that’s not what my comment was referring to. My comment was a response to the bogus rhetoric you threw into this post as a swipe against the mainstream narrative on the DNC hack. That rhetoric was wrong and misleading, in an a trivially obvious way. I get you may not want that to be the focus of this thread, but you chose to put it in the post so you can’t be surprised/upset at people pointing out it was nonsense.
I intend to connect up to the DNC hack, at which point, I’d welcome your criticism on such points.
What’s bogus about pointing out the glaring contradiction in CrowdStrike’s self-serving statement? How does the police associating some burglar with other burglaries blah blah blah have any bearing on this story? Somebody needs to take a pill and calm down.
Yeah, this is really an absurd attack. Your bogus analogy is just plain dumb. It makes no sense, unless your superb burglar is the only burglar who is really good at bypassing a particular alarm system. We expect better of you, Brandon. And why so much hostility?
Brandon,
“There is no contradiction between exhibiting superb tradecraft and being readily identifiable.”
In burglary or hacking, unless the person possessing the “superb tradecraft” wants to be identified there is obviously a tremendous contradiction between “exhibiting superb tradecraft and being readily identifiable.” Generally, burglars and hackers don’t want to be identified and, to the extent they are identifiable without wanting to be identified, they don’t have “superb tradecraft.” Even hackers and burglars with weak “tradecraft” can avoid being identified if they want to. To claim otherwise is just ridiculous.
At the same time, if a person with “superb tradecraft” wants to “readily identifiable” you may want to ask yourself why that is.
So Brandon… that means that Crowdstrike could not find anything so that is how they immediately knew it was the Russians?
Not at all. It is hardly remarkable Crowdstrike would have been able to find signs of intrusion. That they were able to identify two separate groups as having broken into the network should surprise nobody.
As for associating those groups with APT-28 and APT-29, Crowdstrike’s identification was likely due to IP addresses, name servers, choice of target, tactics and many other factors. None of that would be enough to identify the group on its own, but comparing it to other cyberattacks could well make it reasonable to conclude the groups were APT-28 and APT-29. The simple reality is if you commit enough crimes, you are probably going to create patterns which can be used to connect many of those crimes.
Whether or not Crowdstrike’s identification was correct, I can’t say since I don’t have the information on how they made the connection. What I can say is it is completely unremarkable to be able to associate an attack with a group who exhibits superb tradecraft. Quite often, being more competent makes it easier to identify your handiwrok.
Brandon, I urge you to consider that a really professional hacker, such as a state intelligence operative, will scatter false flags about the crime scene.
The world class superb Russki cat burglar dropped his wallet at the scene and was caught on video before he pulled down his balaclava.
He had a dark skin: Nigerian!
Steve, thanks for this, an interesting post.
I find this to be one of the most intriguing bits of information in your post:
“On January 4, 2016, a class action lawsuit was filed against root9B by investors who alleged that root9B’s officers and directors had made material misrepresentations, including false claims to have detected a ” sophisticated state-sponsored Russian hacking attack”.
CrowdStrike has a lot to think about. They could go down like a hot air balloon run out of gas. Investors tend to really p*ssed when they discover that they have been fleeced. CrowdStrike claims that they have no plans yet for an IPO. Strange, you would think that they would take advantage of the favorable publicity this past year.
“facial” absurdity…
“farcical” absurdity?
facile, I thought.
“Facial” makes good sense. Facial absurdity is absurd on its face, or primae facie absurd.
Reblogged this on I Didn't Ask To Be a Blog.
Crowdstrike’s DNC “hack origin” 176.31.112.10 was indeed used too in the 2015 German parliament breach https://netzpolitik.org/2015/digital-attack-on-german-parliament-investigative-report-on-the-hack-of-the-left-party-infrastructure-in-bundestag/
From there there were crumbs towards France and Pakistan and “CrookServers”.
The FSB or GRU using the same server IP on two different huge political hacks it too implausible even for a script kiddies first baby steps, but not for pied piper Crowdstrike and its followers.
(soft coded) IP addresses can be spoofed https://en.wikipedia.org/wiki/IP_address_spoofing; even hard coded MAC addresses can be too: https://en.wikipedia.org/wiki/MAC_spoofing
All groupies of Crowdstrike and the present US IC leadership must logically conclude that the FSB and GRU stupidly were not doing this for either the Bundestag or DNC hack.
It may be noted that this address is under RIPE NCC, a non profit organization that cover EurAsia & the ME: https://en.wikipedia.org/wiki/Regional_Internet_registry
While Crowdstrike managed to raise a lot of money for their cyber software enterprise, John MacAfee (ex-employer of some of their hot shots) goes opposite and promotes mainly new hardware to reduce hacking. Out of his recent 3 predictions about cyber software the first 2 have come true. His last prediction is known to all serious IC units around the globe: ‘3. “Intelligence agencies will finally accept the fact that a sophisticated Nation State can perpetrate any hack and make it point to any Nation or agency that they choose. Attribution for a hack, in this day and age, is statistically, a near impossibility. Hopefully this will motivate our leadership to focus on cyber defense rather than cyber weaponry and abandon the futile and obviously erroneous pursuit of forensic science as a means of identifying a hacker.’ https://www.csoonline.com/article/3155572/internet-of-things/john-mcafees-3-major-cybersecurity-predictions-for-2017.html
Interesting. McAfee is the dean of cyber security, being the first with anti-virus software, over twenty years ago.
Just 20 years? Much more than that. About 30 years ago I installed antivirus on a PC after removing a vitus by manually restoring the MBR of that PC. The virus would modify the MBR (master boot record) of the disk so that on startup it could start a TSR. I sometimes miss the simplicity of MS-DOS…
I can’t remember whether it was MacAfee or Norton AV.
But this was around 1987, not 10 years later.
No, not “just 20 years” but _over_ 20 years ago. John McAfee founded McAfee & Associates in 1987, but I was not aware of the precise date but only that he was the first. Symantec did not offer their antivirus software until 1990, all of this according to i-net sources.
Oops sorry I misread the ‘over’ bit 🙂
So the AV must have been McAfee. And it can have been early 1988, because I think it was the Ping-Pong virus. I just remembered because it was the PC of a fellow student during my first year of Computer Science (1987/1988).
“..abandon the futile and obviously erroneous pursuit of forensic science as a means of identifying a hacker.’”
==== ===
I am going to say it. If McAfee is right, the public posturing by Dmitri Alperovitch and CrowdStrike verges on dishonesty. CrowdStrike, a venture capital start-up,is in the position of making an Initial Public Offering to the great profit of the investors and organizers. The time is opportune. But this means running the gamut of an SEC application and public comments. CrowdStrike says it has no IPO planned at present. Possibly, they intend to remain a private concern. By this, they avoid much regulatory compliance and scrutiny.
Is there any source supporting the idea Crowdstrike thinks this was a case “of exclusive use of malware by a nation state”? I haven’t seen anyone post one on this site so far. If Crowdstrike believes it, they’re dumb, but if not, this is a really lame straw man.
Yet, through private placement, they have raised $265 million, through a limited number of investors (as per law). These types of investors invest on the expectation of a successful IPO, with the prospects of returns in multiples of their original investment.
????
such investors invest as “sophisticated investors” and have much more limited rights to claim misrepresentation than the public. None of them will ever sue Crowdstrike.
Crowdstrike is the only PC Defense company that was ready willing and able to support a false attribution to the public that encapsulated the US and Natos foreign Policy. While Mcafee was a Darpa product, it wasn’t about to go and lie to maintain such a policy. A policy which is buoyed up to continue the Containment of Russia.That is clearly demonstrated by Alperovitch down to Crowdstrikes ExFBI staff,Henry and Chabinsky.
From His previous state of mind( its not a malware problem its an advesary problem) in relation to Russia and China to its current case This is no different than hiring a room full of mercenary black hat to do your dirty work. NSA CIA do this all the time. Once you understand that then you see why there have been no consequences, no valid and public scrutiny of those servers by either LE or publicnor will there be any.. there will be none whatsoever.If he we directed to say China, NK, Syrian Electronic Army, there would be no hesitation either.and like an indistinguishable photoshop pic from a real one..he can do that. Cs has all the Russian codes. No other PC company can claim that.
It is more serious than the US going into Iraq with a presentation at the UN by Powell of powerpoint and fake vials of chemical agents. It’s far far worse because we wont even get that courtesy, that luxury as it were, of a powerpoint presentation, crying children at a Senate hearing, ,or UN review.
It’s far more cost effective than anything we have ever seen before.
It’s completely based CS’s say so.It’s completely evidence free.
Think long and hard about that. What does evidence free look like.? a pair of empty hands stretched outwards, giving nothing and ready to receive or worse.. take. It looks like the Spanish Maine, the Gulf of tonkin, Like Iraq ,like Syrias White Helmets, like Libya, followed endless human harvests.
Think long hard and deep where Crowdstrike has led you.
sysconfig:
It would help if people didn’t flood this site with obviously false claims. As much fuss as people like to make about the DNC not giving the FBI its servers, it did provide images of their drives which would contain practically all the same information as turning over the actual devices. It would have been better if the DNC turned over the actual devices as there are some things images would not be sufficient for, but that’s almost on the level of splitting hairs. There’s little reason to think the DNC’s decision not to turn over the devices themselves would change anything.
As far as the record shows, the FBI has, for all practical purposes, the same forensic information Crowdstrike had. The idea all anyone has to go on is Crowdstrike’s word is a complete fiction.
BS:”As far as the record shows, the FBI has, for all practical purposes, the same forensic information Crowdstrike had. The idea all anyone has to go on is Crowdstrike’s word is a complete fiction.”
=== ===
Not true, Brandon. CS had the hard drive. The FBI repeatedly asked for the computer and were refused. We been over this before – snip
This article might shed some light:
https://www.theverge.com/2017/1/5/14178806/fbi-dnc-hack-server-examined-forensics-russia
As I mentioned before, the FBI had some reason to believe that the DNC was being hacked by Russians, before Crowdstrike became involved, from some means other than examining DNC’s system:
“We also know that the FBI suspected Russian involvement in the DNC breach long before CrowdStrike got involved. According to the Times’ recounting, the first contact between the FBI and DNC came in September 2015, a full seven months before CrowdStrike was contracted. The Times article doesn’t detail exactly what tipped the FBI off to the breach, but it’s fair to assume it was some version of the threat-sharing systems used at NCCIC and similar centers.”
mpainter, do you deny the DNC publicly stated it turned over drive images to the FBI? If not, are you accusing them of having lied when they made that statement?
If the answer to both questions is no, then I’ve not made anything up.
Posted yesterday on previous thread:
Here Brandon, this should help you get up to speed. In fact, I recommend that you read the whole posting/comments from last month. Mr Pete posted this:
Posted Sep 3, 2017 at 10:04 PM | Permalink | Reply
A byte-for-byte copy of a drive is insufficient as a forensic copy, at the FBI level and above.
It’s sufficient for those who only want to see what is *currently* written.
However, AFAIK (as a former drive recording technology expert in the commercial realm) there are most likely classified methods available to detect what may have previously been written to the drive.
My conclusion: most definitely The FBI should have taken possession of the actual disks.
Steve: very useful comment. The contrast with police taking Climategate server is pretty striking, especially given the fallout of DNC attribution.
That does nothing to show I’ve made anything up mpainter. People may dispute how important having access to more than disk images would be, but that is not a matter of making anything up. It certainly isn’t a matter of people’s conclusions being “completely based CS’s say so” or those conclusions being “completely evidence free.”
You persist in citing a false equivalence between hard drive and retrieved forensics so provided by CrowdStrike. Yet this equivalence is invented by yourself; made up, fabricated. It is not a simple matter of disagreement, it is your own disconnected world that you occupy.
Brandon doing his very best not to be testy:
(1)”As far as the record shows, the FBI has, for all practical purposes, the same forensic information Crowdstrike had.”
(2)”The idea all anyone has to go on is Crowdstrike’s word is a complete fiction.”
Assertion (1) is incorrect.
Assertion (2) is correct.
Yes. June 20 is the first CS memo. It would be of course too soon after the claimed June 17 hiring to have ready product. This makes the “never Trumper” client significant to the timeline. If that client is fiction the start date of Clinton’s hiring of Orbis/Steele is also fake and would have to be pushed back to early June at least if not earlier. I hope investigators press on the identity of Orbis’s alleged first anti-Trump client. Just as important a question is who approached whom. Did Orbis approach the never Trumper or the Clinton campaign as he did the FBI and Mother Jones and others? The motivation for the creation of the Steele dossier and its marketing are key pieces of evidence as to its credibility and to its origin.
Right, Ron, the 20 June date indicates an earlier genesis for the first Trump memo.
If Fusion GPS indeed engaged Christopher Steele on/about June 17, this gives a solid indication that another party initiated the dirty dossier from Steele. We can also assume that this other party made it clear to Steele that he was expected to come up with the “goods” on Trump. If Steele cooperates with the Mueller probe, he will be forthcoming with all these details.
I am hopeful that Steele will cooperate, else why would he meet with Mueller’s goons? Also, Steele will be subject to pressure from the May government who certainly owe Trump a cooperative attitude.
Actually, the key pieces of evidence for the credibility of the Steele dossier are actual pieces of evidence that support the claims in the dossier. My guess is that Steele doesn’t have any evidence. My guess is that he won’t reveal his sources or if he does his sources won’t have doodly squat to back up their claims. Fiction is hard to prove.
Alperovitch had been active on the DNC system for quite sometime; finally they re-imaged everything to wipe out any malware (like G2’s stuff). A lot of interesting HDD sectors will be overwritten in that process; only some will have older traces left. Old back up full disk images would be good to see…. again crumbs towards that Russian amateur clown make-up, as Alperovitch couldn’t find anything better.
Timeline:
Prior to April 2016 Fusion GPS, a pro-Dem research firm was allegedly hired by wealthy “never Trumper.” Fusion GPS hired Christopher Steele/Orbis .
May 5, 2016 — Crowdstrike arrives at DNC and installs Overwatch software and detects breach.
May 25, 2016 — Last dated WikiLeaks DNC email.
June, 2016 — Fusion GPS/Steele/Orbis switch clients from never Trumper to presumably Hillary Clinton or DNC.
June 6, 2016 — HRC clinches the Democratic Party nomination.
June 9, 2016 — Trump Jr. meeting with Russian lawyer Natalia Veselnitskaya, who promised Clinton emails. She worked for two years with Fusion GPS.
June 10, 2016 — First Fusion GPS/Steele memo is submitted to Dems stating Trump has been being groomed by Russia/colluding for prior 5+ years.
June 10-12, 2016 — Crowdstrike rebuilds DNC IT system with new passwords.
June 12, 2016 — Assange tells interviewer that WL has new emails “related to Hillary Clinton.”
June 14, 2016 — Crowdstrike and DNC announce two Russian groups, Cozy Bear (FSB) and Fancy Bear (GRU), independently hacked the DNC. The former arrived the previous summer and had been hacking for a year. The later group arrived just before CS arrival on May 5 and, according to CS’s Alperovitch, only exfiltrates one document, the Trump opposition research.
June 15, 2016 — Guccifer 2.0 introduces himself to Gawker and claims he is responsible for both DNC hack groups and produces the Trump opp doc and other DNC docs. G2 also claims the WL was regarding his release of the DNC docs to them. But when the WL DNC docs are revealed 5 weeks later none are a match to Guccifer 2.0 releases, which goes largely unnoticed to the media and US IC, who have already swallowed G2 as both the hacker and Wikileaker of DNC. He claims to be Romanian but intentionally changes the Trump oppo document by placing it in an MS Word template with the name of the first Russian head of secret police using Russian language setting. Besides using Russian tools Apt 28/29 he also uses Russian VPN to forward emails to news media.
Question: Since clearly Hillary benefits from proving Russian’s hacked DNC, which is by June 6, essentially part of the Clinton Campaign, and Clinton knows from Fusion GPS that Trump is colluding with Russians, why not bring in the FBI immediately and confirm and document the heck out of the Russian incursion that she knows can be hung around Trump’s neck?
one constraint on the DNC raising security issues too loudly in June 2016 is that Comey hadn’t yet deep-sixed the Hillary email investigation. Cheryl Mills had caused the Clinton server logs to be destroyed – thereby enabling Comey to say that there was no evidence that the Clinton server had been hacked (since the evidence had been destroyed) while obtusely pretending not to notice the obstruction of justice – an issue that Comey had used as a bludgeon against Martha Stewart and others,
first Fusion memo is dated June 20. Retaining of Steele by GPS is around June 17. No evidence thus far of work product for never Trumper. This leg not documented so far and may (or may not) be a fiction
Come on, Ron. Everybody knows that if you claim to be Romanian and you ain’t, then you must be a Russian spy.
Here is an interesting and cogent analysis from folks at the left wing Intercept. It’s from back in December, but I don’t think a lot has changed in the quality and quantity of the publicly available evidence:
My reply flew over here.
while obtusely pretending not to notice the obstruction of justice
What is your evidence that Cheryl Mills engaged in obstruction of justice? I have seen none, and I think the same applies to Comey.
Cheryl Mills organized the destruction of documents on Clinton server backups, including server logs, in the face of a preservation order from congressional committee. Evidence is plain as day.
Evidence is plain as day.
And that evidence is? Is there something in the FBI report that tells us that? And, if so, why did none of the Republicans point that out at Comey’s testimony?
http://www.politifact.com/truth-o-meter/statements/2016/oct/09/donald-trump/donald-trump-says-hillary-clinton-deleted-33000-em/
The FBI’s investigation did find several thousand emails among those deleted that were work-related and should have been turned over to the State Department. However, FBI Director James Comey said in a July 2016 statement that the FBI investigation “found no evidence that any of the additional work-related emails were intentionally deleted in an effort to conceal them.”
Comey added in a later congressional hearing that the FBI learned no one on Clinton’s staff specifically asked the employee to delete the emails following the New York Times story and subpoena. Rather, the employee made that decision on his own.
Comey (June 2017) – NBC News – 2017-07-08 – James Comey Hearing: Full Transcript of Ex-FBI Chief’s Testimony
Ergo: The DNC did not turn over the server(s) to the FBI so that the FBI could examine them.
And the FBI also did not receive the content, so neither did they get full disk images.
Jaap Titulaer, thanks. We have had several commentators who insist that the DNC provided the FBI with “full disc images” (Brandon for one). So you cleared up an issue.
mpainter, not so fast. The article that Jaap T cited from Medium.com here, says CS turned over the image, as Brandon pointed out in another comment today. Looking at that article it hyperlinks the words “forensic image” to a Washington Times article here where they report CS emailed them a response on this question.
But in the Times article is very skeptical of CS’s claim pointing out Carr’s analysis and the fact that both Comey and DHS Secretary Jeh Johnson said they were refused access.
So the source of the “forensic images” claim is CS, along with their assertion “we fully cooperated with every U.S. government request.” The government agencies have a very different story but the press and congress are having a hard time realizing this and getting the truth.
It is possible bureaucrats at the DNC did offer to let the FBI look at the server and the FBI declined or made it impractical.
In most instances it would be the other way around. But here, the FBI and the contractor could be more on the same page than the DNC officials who are involved in day to day matters.
Ron, I will go by Comey’s testimony until I see a more reliable source that refutes it.
Follow TM: “It is possible bureaucrats at the DNC did offer to let the FBI look at the server and the FBI declined or made it impractical.”
It is the contractor, CS, that is making the assertion of full cooperation and providing the server image. And, it is the FBI director and DHS secretary who claim their help was rebuffed. Director Comey specifically confirms under oath that they did not receive the server content.
mpainter, I’m not willing to rely on either CS’s or Comey’s word over the other or willing to let them off the hook when their stories don’t match. I want somebody tough, smart and non-partisan asking questions of all parties.
Comey’s testimony is not very helpful. How could the FBI have gotten “relevant forensic information” and his people “had gotten the information from the private party that they needed to understand the intrusion by the spring of 2016.”, without getting any “content”. What Comey vaguely described could possibly have included complete disc images.
Comey’s various testimonies before congress have not impressed me as being very intelligent or informative.
@ Don Monfort
Easy, it simply means that people at FBI management level were ready to, or forced to, accept the conclusions of a third party, as to who-did-it and in order to understand what happened when (according to same third party). It is enough to be able ‘to understand the intrusion’. So the information received was ‘relevant’ for that.
Just without being able to corroborate it…
What the FBI received may very well be similar to that what CrowdStrike has published for public consumption, although I do expect that the FBI has gotten a slightly longer or more detailed & technical report. Maybe the FBI even received some forensic samples, such as copies of the malware binaries and any scripts.
You just can’t check whether any of it is real.
It is like the crime scene (and say the body & murder weapon) is off-limits to the police. They get some summary reports, but may or may not have received any underlying details, like the DNA findings, the weapon analysis etc. And they certainly did not get some stuff, like say no crime scene photos or the actual witness statements. And the police also has no way of verifying that any of the details that they have received are actually based upon (the original) reality or one has only very limited ability to do so (say the identities of some of the witnesses are hidden).
Sorry but, that’s not possible IMHO. ‘No content’ simply means no content or practically no content (for purposes of a verification and second opinion by FBI Cyber).
A forensic disk image is a full copy of the entire disk, for all partitions of that disk, including hidden partitions, and for all sectors of every partition, so not just all files but including those parts that still have bytes on them from files already deleted (deleted according to the file system).
If this is done for all disks in a server and any disk attached (across network) to the server then and only then can one speak of a full set of forensic disk images.
Of course even such an image can be manipulated, for example you can install the malware on a forensic image or prior to making that image.
Or you make a backup of most of the files on a server and restore that on a clean disk image, then correct it here & there, prior to making a (faked) ‘forensic’ disk image.
It is always better to have access to the original hardware, but forensic disk images are a close second best.
And you have to be careful not to disturb the original, so you would usually work on a forensic disk image (but of course only on copies that your team has made themselves).
All files on the original servers would be on them (by definition), so it doesn’t make sense to really give the FBI a full set of forensic disk images, yet refuse them access to the original servers.
Jaap: “You just can’t check whether any of it is real.”
If you can’t check if it is real, it is not forensic evidence, forensic samples, or forensic information. It’s more like hearsay.
You said:”It is always better to have access to the original hardware, but forensic disk images are a close second best. And you have to be careful not to disturb the original, so you would usually work on a forensic disk image (but of course only on copies that your team has made themselves).”
Exactly correct. If the investigator has not made the copies himself, then they are not forensic. They are just some crap somebody gave you. So in his testimony, if the information Comey was referring to was not FBI verified copies of the actual disks, then he should not have been calling it forensic information. And if you don’t have any “content” from the disk, you don’t have any forensic information. Period.
PS: Comey said the FBI “had gotten the information from the private party that they needed to understand the intrusion by the spring of 2016.”
Logically and legally the information that they needed for FBI/law enforcemet purposes was complete forensic disc images.
In fact there were chemical weapons in Iraq, left over from its war with Iran. Found in missile context after the US took over.
And used some on Kurds, hence the UN’s establishment of a no-fly area.
(And keep in mind that Iraq had a nuclear reactor back a ways, Israel took it out.)
In general, people were conned by Saddam Hussein’s claims – he had intent to produce WMD but hadn’t performed. And showed aggression by invading Kuwait.
(And there’s a question of what might have been spirited out of Iraq when the US military took it over but did not have full control. Syria would be one suspect for destination, though its nuclear reactor that Israel took out was more likely designed and fueled by North Korea.)
January 7 2015 the FBI (Comey) attributed a (Sony) cyber breach to a (hostile) foreign nation without substantial evidence, North Korea in that case. Private cyber sleuths aired their strong reservations: http://marcrogers.org/2015/01/07/response-to-the-latest-sony-comments-by-fbi-director-comey/
Kaspersky Labs exposes quick and sure cyber attributions a la Alperovitch: https://www.virusbulletin.com/conference/vb2017/abstracts/walking-your-enemys-shadow-when-fourth-party-collection-becomes-attribution-hell/ and https://theintercept.com/2017/10/04/masquerading-hackers-are-forcing-a-rethink-of-how-attacks-are-traced/
They point out that some Israelis don’t hesitate to use false cyber flags through 1 on 1 code copying. Some non governmental groups might have similar little constrain.
Quote from DumbStruck :
CrowdStrike has a corporate motto: “You don’t have a Malware Problem, You Have an Adversary Problem.” The ethos behind this motto, as explained by Adam Meyers, who runs CrowdStrike’s Global Threat Intelligence Team, is the notion that by focusing on the adversary “you are dealing with the problem, not just a symptom of the problem. Malware deals with the symptom.” Adversaries, Meyers notes, “are the humans behind the attacks. We spent years in security focusing on malware and exploits and techniques, but not on who is perpetrating them. There are humans behind the attacks, so we watch for patterns, use intel to zero in on the human element. We ask who they are, what their motivation is and what types of things they are likely to do in the future.”
=== === === ===
Quote from John McAfee:
“Intelligence agencies will finally accept the fact that a sophisticated Nation State can perpetrate any hack and make it point to any Nation or agency that they choose. Attribution for a hack, in this day and age, is statistically, a near impossibility. Hopefully this will motivate our leadership to focus on cyber defense rather than cyber weaponry and abandon the futile and obviously erroneous pursuit of forensic science as a means of identifying a hacker.”
=== === ====
McAfee left the company that he founded in 1994. He employed none of the present crop of cyber fixers at CrowdStrike.
Excellent work Steve!
Illustrative, illuminating and very very intriguing!
I’m looking forward to the next post in this series.
Some facts which should yield some understanding of this CrowdStrike/DNC/FBI affair:
Shawn Henry joined CrowdStrike in 2012 as the head of one of their divisions, leaving an executive position in the FBI where he had been a protege of Mueller.
Comey and Mueller were as thick as thieves, we all know. So this CrowdStrike/DNC/FBI affair has swamp creatures slithering al over it. If there is some confusion about what CrowdStrike provided the FBI, or whether or not the FBI sought certain cooperation from CrowdStrike, or just exactly where the truth lies, then I put that this confusion is no accident but is deliberately sown.
Comey and Mueller were as thick as thieves, we all know.
It’s not so much what we don’t know that gets us in trouble, it’s what we “know” that just ain’t true.
It’s what we learn by following our nose that gets the swamp crawlers in trouble.
And with the swamp still draining we have netted Comey, Mueller, McCabe, Strzok, Nellie and Bruce Ohr, with more to come. Sniff, sniff, there’s another one.
http://www.nationalreview.com/corner/453092/scandals-collide-dossier-dnc-server-perkins-coie
March 2016 – Hillary for America campaign and DCCC come under cyber-attack from Apt28/Fancy Bear
March 29, 2016 – Paul Manafort joins Trump campaign. This week it is revealed that Manafort was a Russia liaison for used by the Podesta Group, which was involved in the Uranium One-Clinton deal. Thus we can assume that John Podesta and Hillary knew immediately of Trump’s Russia vulnerability on this date.
April 2016 – Clinton hires Fusion GPS to do Trump Russia research.
Revealed this week, the Clinton campaign, not a “never Trumper,” was the original client for the Trump dossier.
May 2016 – The same law firm that hired Fusion GPS for Clinton hires Crowdstrike for DNC.
June 14, 2016 – Crowdstrike and DNC announce Russian Attack
June 15, 2016 – Guccifer 2.0 announces he is the DNC, DCCC and HfA hacker and Wikileaks source, waving the Trump opposition research report (with Russian metadata).
The smoking gun could be Imran Awan. We just have to wait.
2016-06-09 Trump Tower meeting
http:// http://www.businessinsider.com/steele-dossier-trump-russia-hillary-clinton-dnc-tower-meeting-2017-10?international=true&r=US&IR=T
2017-07-22 Fusion GPS and the Russia connection
http://www.zerohedge.com/news/2017-07-22/new-media-normal-manufactured-news-hire
2017-10-18 Fusion GPS pleads the 5th …
2017-10-19 Trump poses a question
http:// dailycaller.com/2017/10/19/trump-questions-whether-fusion-gps-was-paid-by-russia-fbi-or-democrats/
Russia: check, see above
2017-10-25 Clinton campaign, DNC paid for research that led to Russia dossier
https://www.washingtonpost.com/world/national-security/clinton-campaign-dnc-paid-for-research-that-led-to-russia-dossier/2017/10/24/226fabf0-b8e4-11e7-a908-a3470754bbb9_story.html?utm_term=.bcc90639d0e3
Democrats: check
FBI: …? [waiting for House investigations which just started]
Who was the “never Trumper” who originally funded the Trump dossier? It turns out that there was none.
Reported yesterday, the news web site The Washington Free Beacon (which supported GOP presidential candidate Marco Rubio) hired Fusion GPS for Trump opposition research but nothing about Russia. Rubio also denies receiving any of the research, “Or I would have used it,” he said with a wink.
Mark Steyn wrote and excellent summary of the whole Russian dossier timeline. It’s also with Mark Steyn’s wit so you can laugh at the ridiculous ironies through the whole unbelievable saga. The key is the hiring of intermediaries as cut-outs to hide the flag. This was every bit an active measures campaign induced to be adopted by the eager US IC and then MSM.
To add Guccifer 2.0 as being hired by Fusion GPS or Perkins Coie, (who got 5.6 million from Hillary to hire Fusion GPS and others), becomes less and less nutty. It is now right in the contenders for the highest plausibility.
We don’t know yet, if ever we will, how much of the money paid to Perkins Coie for “legal services” went to Fusion for making up the dirty dossier. There were very likely legitimate legal services that P&C were performing for the campaign and the DNC. Hopefully, the Congressional investigators will be able to get Fusion’s bank records. And maybe a FBI or Special Counsel investigation will get to the bottom of this scam.
I think this is a more useful timeline:
http://dailycaller.com/2017/10/28/finally-a-definitive-timeline-showing-when-clinton-dnc-started-the-russian-dossier/
Here is some info that covers one month of payments to P&C gleaned from FEC records:
“April: Perkins Coie, using money from the Clinton campaign and DNC, hires Fusion GPS. Marc Elias, a Perkins Coie partner and general counsel for both the campaign and DNC, would serve as the bagman.
That month, Federal Election Commission records show that the Clinton campaign paid Perkins Coie a total of $150,000 for legal services. The DNC paid the firm around $107,000. It is unclear how much of that went to Fusion GPS. Both the campaign and DNC would pay Perkins Coie hundreds of thousands more dollars throughout the campaign.”
Fusion GPS has dropped resistance to House Intelligence Committee subpoena for bank records. Will now provide pertinent records. The truth emerges bit by bit.
To be explicit, we shall now learn how much of the millions paid by DNC/Hillary to their law firm went to Fusion GPS and how much of that was paid to Steele. Maybe we shall learn how much Steele paid his informers, or whether he kept it all. Former British ambassador to Russia Wood of course was in on the take.
Don, Steyn concludes that we would be better off without the US IC, (bathwater and baby). Compared to that I think my proposal for re-alignment and stepped up senate oversight is rather tame.
Trump’s acquiescence to the US IC for one last cleaning of the JFK file is disappointing. After 54 years there is no legitimate reason for it. By comparison the Nuremberg Trial files were closed for only 50 years, establishing an international standard. America’s stock did not rise by ignoring further postponement. Granted it could be embarrassing for someone still alive. Curt Waldheim certainly was not a fan of the Nuremberg declassification.
I agree with Steyn concerning the U.S. intelligence community, particularly the CIA and the NSA. These should be governed by a board that has complete oversight and authority. New provisions that protect against excess should be formulated.
Maybe Trump will do something. I, for one, am disgusted by our FBI, DHS, and IC. It is wrong that someone like corrupt James Comey should be installed with complete authority over these institutions.
Ron, after eight years of Obama the agencies were highly politicized. Obama’s stooges hired and promoted the people with the right politics, meaning left politics. The military suffered from the same political interference and influence. Trump and his people are well aware of the problem. The political appointees will be ditched and the remaining slobs that can’t be easily fired will get reprogrammed, or assigned to boring dead end duty where they can’t do any harm. It’s our turn to politicize the agencies. That’s how it works. Civilian politicians are in charge of the military and intel institutions. Congress exercises oversight. How else would we do it?
Last I heard Trump ordered the agencies to release the JFK files only redacting the names and addresses of living individuals. That seems quite reasonable to me.
Another interesting aspect of all of this: Hillary/DNC pays for and gets a dirty dossier on Trump and the same is provided Comey so that he can obtain FISA warrants against Page, Manafort, and ? (Unmasking galore). Looks like collusion between Hillary and Comey and ?Russia (more to come?) while at the same time Comey is writing her Get Out of Jail Free card.
It will all come out. Hillary has been unusually quiet these past three or four days. The world awaits with bated breath her thoughts on this.
Perkins, Coie may have told her to shut up, once and for all.
Trey Gowdy, Republican Chairman of the House Committee on Intelligence, today stated on Fox News that Perkins, Coie was “money laundering” for Hillary/DNC. That is criminal. I predict that he will subpoena records, documents, correspondence, etc. from P,C, the Dems, Hillary and whomever. Both Podesta and Shultz have testified before Congress that the Dems did not pay for the Dirty Dossier. They are in a well full of sheet.
The reason that the DNC paid Fusion via Perkins, Cole is so that Podesta and Schultz could later testify that the DNC hadn’t paid for the research. Even now, it is possible that Perkins Cole would not be required to answer questions covered by attorney-client privilege – such as “To your knowledge, did Ms. Schutz know about the Fusion contract?
Perkins Coie paid by Clinton campaign and DNC (which was controlled by Clinton campaign). Hillary has a lengthy practice of using lawyers to do her dirty work. She used lawyers as assistants (Cheryl Mills, Heather Samuelson), thereby purporting privilege over otherwise non-privileged actions e.g. in destruction of emails, destruction of servers, destruction of backups. Mueller pierced privilege for Manafort’s lawyer but DOJ and FBI made no attempt to pierce privilege of Cheryl Mills, Heather Samuelson, David KEndall.
How is doctor-patient privilege legally protected in the US compared to client-lawyer privilege?
Here in India unscrupulous politicians have another a standard trick to keep out of jail in case of arrest: they immediately claim heart problems – which are serious but hard to check – and go to some private hospital room instead.
RE: Steve McIntyre, “Mueller pierced privilege for Manafort’s lawyer but DOJ and FBI made no attempt to pierce privilege of Cheryl Mills, Heather Samuelson, David KEndall.”
And now Manafort’s suing Mueller. I’ve lost track of both sides on this one.
http://nationalpost.com/news/world/paul-manafort-is-suing-robert-mueller-claiming-he-overstepped-his-authority-in-russia-investigation
https://www.wsj.com/articles/prosecutors-consider-bringing-charges-in-dnc-hacking-case-1509618203
This would be Trump’s DOJ. They think they have enough legal evidence to indict 6 Russians for hacking the DNC.
But don’t get discouraged.
Psh. I’m sure the DoJ is just mindlessly going off things it read in the fake Steele Dossier and assuming the Russian “whiskers” in released files means Russia was to blame.
Will be real fun to watch how they want to prove that those 6 particular Russians hacked the DNC without exposing the NSA’s prime hacking capabilities inside Russian government. Plus to avoid spotlighting NSA, FBI and DNCs lack of Homeland cyber defences. Or keeping Nigerian scammer tools etc. out of the picture.
Only one way: prosecution + defence + judges have to play mum & dumb
Has the clever Sessions figured out a way to subpoena the DNC hard drive? This could be the next step in the investigation. After all, such evidence would be mandatory, would it not?
The noose is dangling, whose neck?
I’ve always wondered what happened to the private investigators Trump said he was sending to Hawaii to find out the truth about Obama’s birth certificate. Probably assassinated by the CIA. Now that he’s president, he should look into it.
Will the government examine the DNC hard drive itself? Not necessarily. Perhaps one of the six defendants is willing to testify against the other five. Or the FBI has found traces of the DNC email on a defendant’s computer. Given the dubious nature of the Russian “whiskers”, it wouldn’t be surprising to find out the government’s case doesn’t depend on this evidence.
If the government subpoena’s the DNC hard drive, they likely must give the defendants access to it, so they can study the evidence against them. (:)) So the server may stay in DNC hands.
In the meantime, the Deep State is slandering Dear Vladimir Valdimirovich and his innocent intelligence services with impunity:
https://www.pbs.org/newshour/world/russian-hackers-used-a-digital-hit-list-to-target-nations-including-the-u-s
Secureworks (?!)found some list file. I claim to have found a list that excludes Don, Brandon and Ivan from receiving Christmas gifts next month.
Fake News rock bottom. This kind of stuff counts as proof in the US these days ??
Even if that really was a GRU wish list, I could congratulate them on targeted hacking, as opposed to the NSA’s full spectrum / all haystacks madness. Too much money, too much megalomania.
AnthonyIndia: If you really prefer the GRU’s selective approach to information collection over the NSA’s, perhaps you’d prefer to live in Putin’s paradise.
As long as the NSA’s surveillance can only be used to put me in jail for terrorism, I don’t have a big problem with it. We are at war with terrorist organizations. If the NSA is going to use their records to prove I intentionally made a “mistake” filling my taxes or am part of a criminal conspiracy to deny climate change, no thank you.
Congress can end these programs anytime serious abuse occurs.
In one of the posts dealing with the “investigations” of the so called collusion with the Russians, I pointed out the fake questioning of Hillary Clinton by Comey. (No transcript or taping — just FBI agents taking notes) This 3 hour sham questioning session was attended by Peter Strzok, who has been found to have sent anti-Trump texts to his mistress. See https://www.wsj.com/articles/muellers-credibility-problem-1512432318 I mentioned at the time that the note-taking was ridiculous because if Hillary did say something harmful, but then denied it, who was going to argue with the President of the US. (the expectation at the time was that Hillary was going to be President)
The WSJ article makes it even worse because someone with an anti-Trump bias was one of those entrusted with taking notes of Hillary’s statements. The idea that either Comey or Mueller are some sort of straight-arrow FBI leaders (and not politicians) is ludicrous.
JD
When it all comes out, it will be seen that the FBI and the DoJ have been corrupted by Obama appointees.
In fact, this is the first task of the new administration, to clean it all up. It may be that Mueller and his goons have expedited the cleanup.
It was also Peter S that altered key portions of Comey’s exoneration letter written well before HRC was even questioned.
I know real hackers though.